Manage Marketing Preferences
If you are marketing to your customers through methods such as email or sms, you need to collect consent to meet compliance with privacy regulations. Build a customized preference center and empower your users to choose their marketing preferences at a granular level.
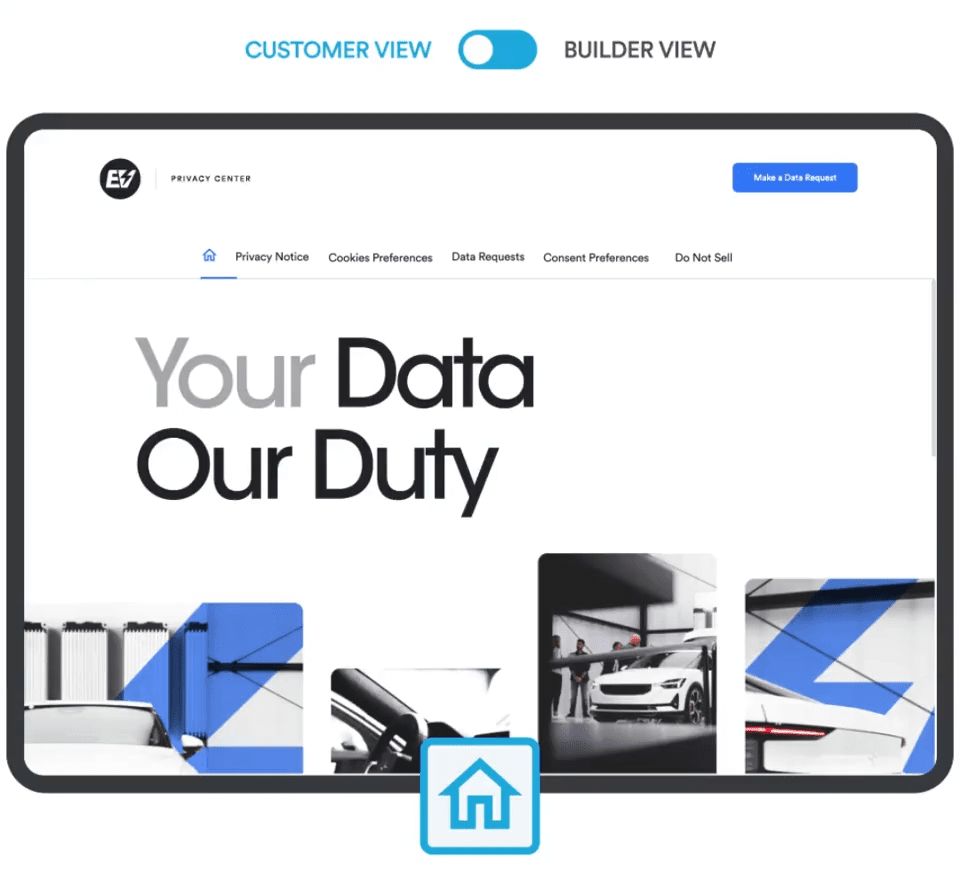
Create a preference center using Securiti’s intuitive builder and offer granular choices to keep opt-in rates high
Create custom consent collection methods from various sources like websites, web-forms, SaaS apps and consent databases.
Use pre-built consent workflow templates to sync consent statuses across 3rd party systems.
Orchestrate consent across an extensive list of applications, such as Salesforce, Microsoft Dynamics, Marketo, MailChimp, MixPanel and more.