Agent Commander Drives High-Impact Use Cases
- Eliminating Shadow AI: Agent Commander brings all unsanctioned and “dark” AI initiatives under centralized governance by not only discovering and cataloging agents and models across the enterprise, but also mapping the underlying data they can access, the sensitive information they interact with, and the associated risk posture. By correlating agent activity, entitlements, data sensitivity, and policy context, organizations gain comprehensive visibility and enforce consistent governance controls across all AI systems, whether sanctioned or shadow, dramatically reducing AI-driven data risk.
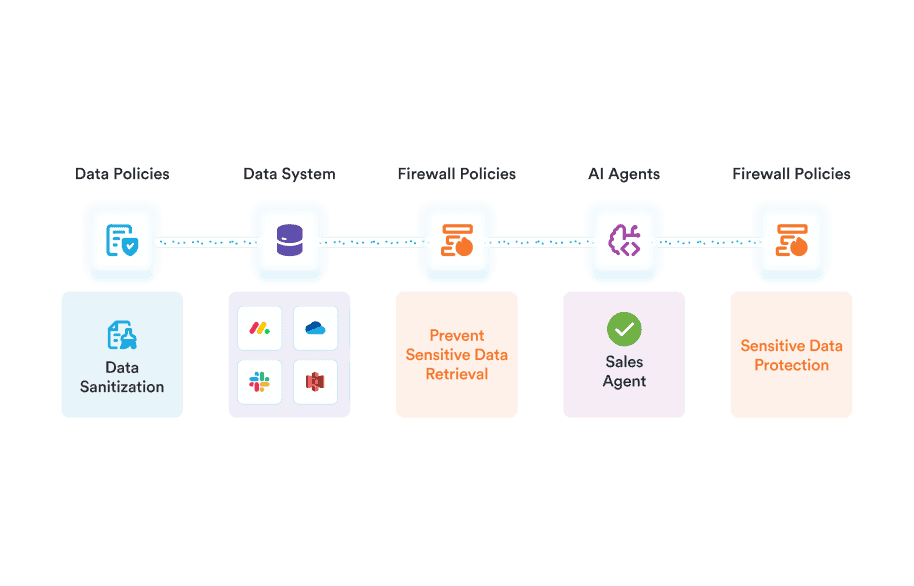
- Securing SaaS AI Agents: Organizations struggle to scale SaaS agents like Microsoft Copilot, Amazon Q, and Gemini Enterprise because underlying data controls are not AI-ready. Missing or inconsistent data labeling, excessive privileges, unmanaged ROT data, and unintended exposure of sensitive information create unacceptable risk. Agent Commander identifies and remediates these foundational data issues so organizations can scale SaaS AI agents safely.
- Securing Custom Agents in the Public Cloud: Like SaaS agents, custom agents require AI-ready data controls. But unlike SaaS agents, organizations must also protect custom agents against external and runtime threats because the burden of these controls sits with the teams building and operating the agents, not a SaaS provider. Agent Commander pairs hardened data controls with context-aware runtime guardrails to defend custom agents during operation, and adds precision “Undo” to recover quickly when agents accidentally write, overwrite, or delete data, enabling safe AI without disruptive system-wide restores.
- Driving Broad AI Compliance: Launching AI agents requires more than compliance with traditional data protection laws. It demands alignment with emerging AI mandates such as the EU AI Act and similar frameworks globally. Manual approaches cannot keep pace with overlapping regulatory requirements. Agent Commander automates control validation, continuously maps technical safeguards to regulatory obligations, and delivers real-time compliance auditability to GRC teams, enabling organizations to deploy AI agents confidently and at scale.
Why Point Solutions Fall Short in the Agentic Era
As AI adoption accelerates, many organizations attempt to secure agents using siloed cloud security (AI-SPM), data security, data resilience, and AI guardrail tools. But these point solutions were not designed for the systemic, interconnected risks of agentic environments.
AI security is not an isolated problem at a specific point in the stack. Risk emerges from the interaction between data, identity, agents, humans, and the actions they take. Tools that secure only one layer inevitably create blind spots.
1. Cloud Security (AI-SPM) Tools: Outside-In Visibility
Cloud security and AI-SPM tools treat AI as another cloud workload, focusing on infrastructure posture, model exposure, and misconfigurations. They lack deep contextual intelligence into data sensitivity, agent entitlements, and runtime data interactions, making it difficult to detect compound risks that emerge across data, identity, and AI behavior.
2. Data Security Tools: No Runtime Control or Resilience
Traditional data security platforms may perform discovery and classification, but are not built to monitor AI prompts and interactions. More critically, they cannot recover from AI-driven actions - writes, deletions, or corruption. Detecting sensitive data does not equate to undoing agent mistakes.
3. AI Guardrail & Prompt-Layer Tools: Runtime Without Data Control
Guardrail tools inspect prompts and responses for injection or policy violations. However, they do not have proactive data controls or prevent agents from operating on high-risk data. And when destructive actions occur, they offer no recovery path.
4. Traditional Data Resilience Vendors: Recovery Without Context
Backup platforms can restore data systems after failure, but they lack visibility into which specific files an AI agent altered. Without granular activity context, recovery often requires broad system restores, which are slow and disruptive. They also do not provide proactive data or AI controls to reduce risk before incidents occur.
Agent Commander represents the first major integration following Veeam’s acquisition of Securiti AI, bringing together market-leading Data Resilience, Data Security, and AI Security into a single converged platform purpose-built for the agentic era.
Built into the Securiti Data Command Center and integrated with Veeam, Agent Commander delivers complete visibility, control, and protection across the entire data and AI estate.
What Makes Agent Commander Unique?
At its core is the Data Command Graph™, a relational intelligence engine that maps connections between data, identities, AI models, and agents across both production and backup environments.
It reveals what other tools cannot see: the toxic combinations where compromised identities, sensitive data exposure, excessive privileges, and agents intersect, and how those risks compound and cascade at AI speed.
No standalone AI security tool delivers this level of contextual data intelligence. No traditional backup platform provides this level of AI-aware precision combined with proactive control.
Agent Commander uniquely unifies three capabilities the industry has never brought together:
- Detect AI Risk with Context
- Protect AI Systems Holistically
- Undo AI Mistakes with Precision
By converging relational data-and-AI intelligence and controls with enterprise-grade resilience infrastructure, Agent Commander establishes the foundation for safe, trusted, and recoverable AI at scale.
To dive deeper: