Prevent Unintended Data Access
- Identify ‘risky combinations’ of files, folders, users and access permissions using graph rules and powerful visualizations
- Understand data sharing risk by analyzing file-level context, including data sensitivity, individual and group entitlements, and regulatory insights
- Easily remediate access misconfigurations using policies that automatically assign security findings to the right teams
Example: Confidential M&A plans accessible by non-finance teams
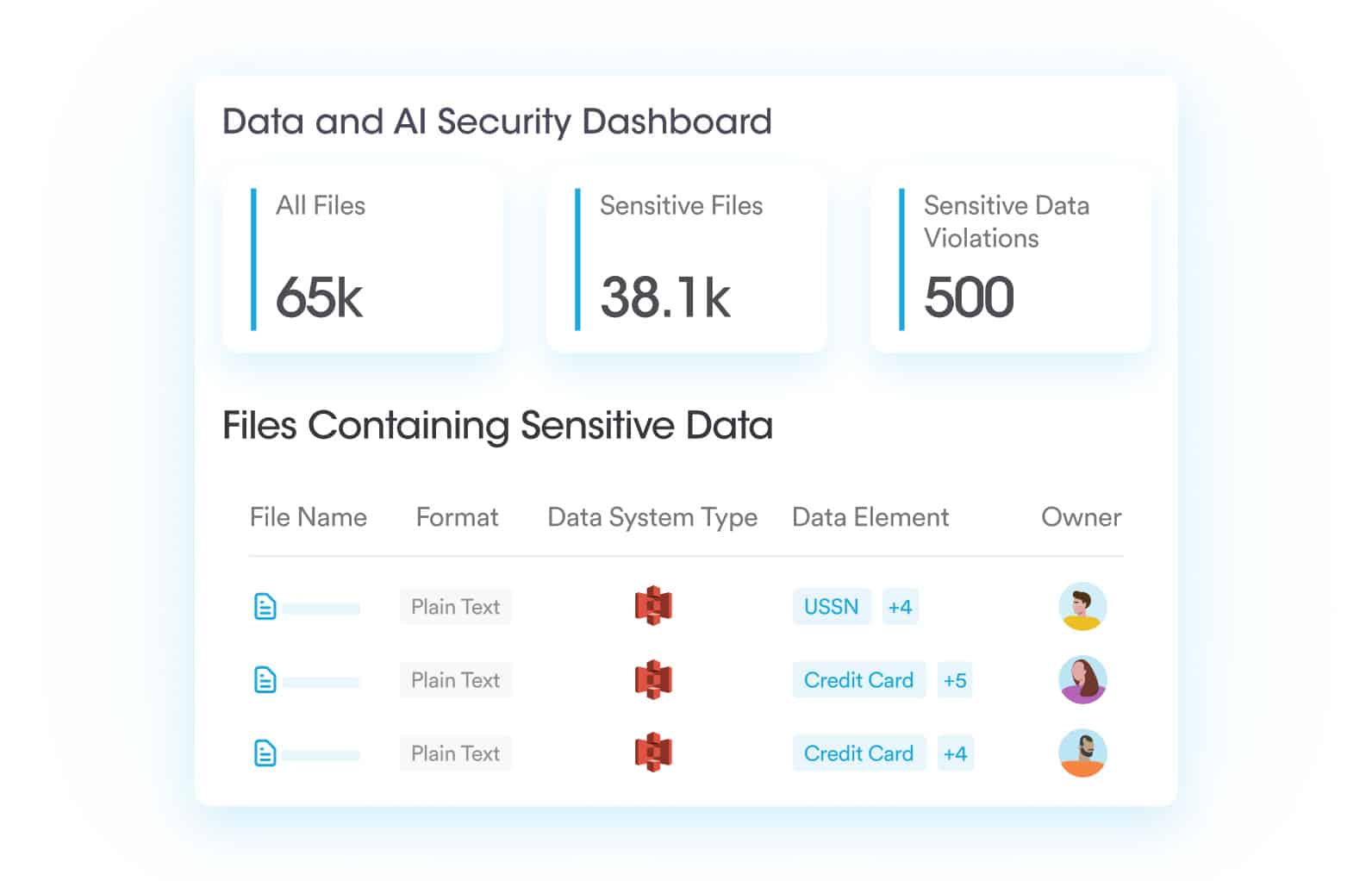
Assess Data Security Posture
- Automatically assess system configuration settings using built-in security best practices for data sharing, protection and compliance
- Review data risk and security violations using built-in dashboards and customizable reporting widgets
- Automatically remediate security posture issues using policies that automatically assign security findings to the right teams
Example: Ensure global sharing defaults to people in your organization
Prioritize Sensitive Data Risks
- Accurately identify hundreds of sensitive data element types and proprietary documents using AI-powered classification
- Analyze configuration security posture risk, detecting files and folders shared too broadly or exposed externally
- Reduce alert fatigue and prioritize toxic combinations of risk by correlating data sensitivity and security posture insights
Example: Enterprise-wide access to sensitive data such as customer contact details
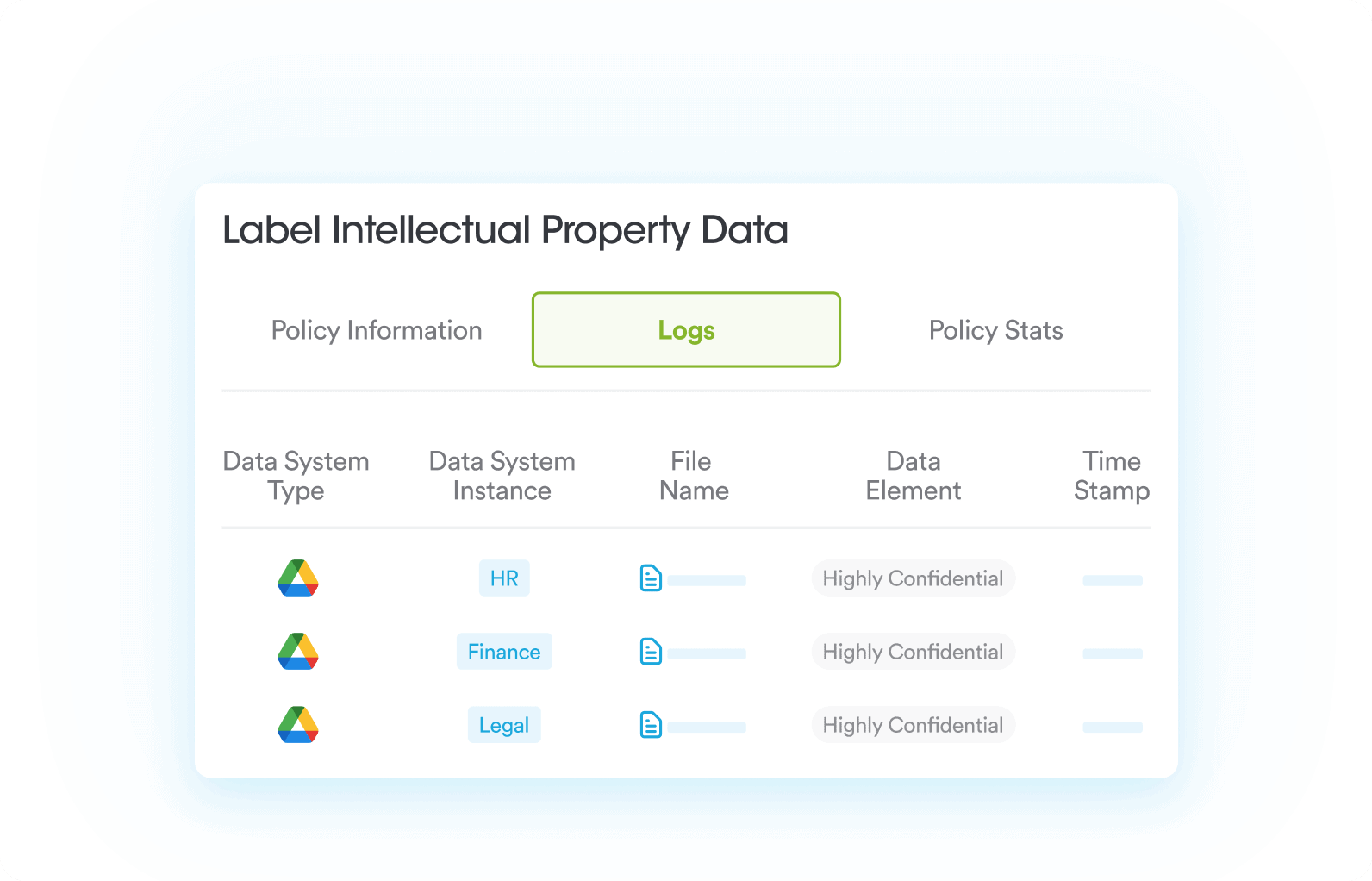
Automate Data Tagging & Labeling
- Automatically label files with precision and at scale based on attributes such as type, classification, ownership, location, security posture, regulations, and age
- Protect company data by excluding files with specific labels from Copilot’s responses to employee queries
- Ensure consistent labeling across hybrid multicloud and SaaS environments using a unified data policy engine
Example: Label files owned by executives as “Restricted” to prevent access via AI Agents
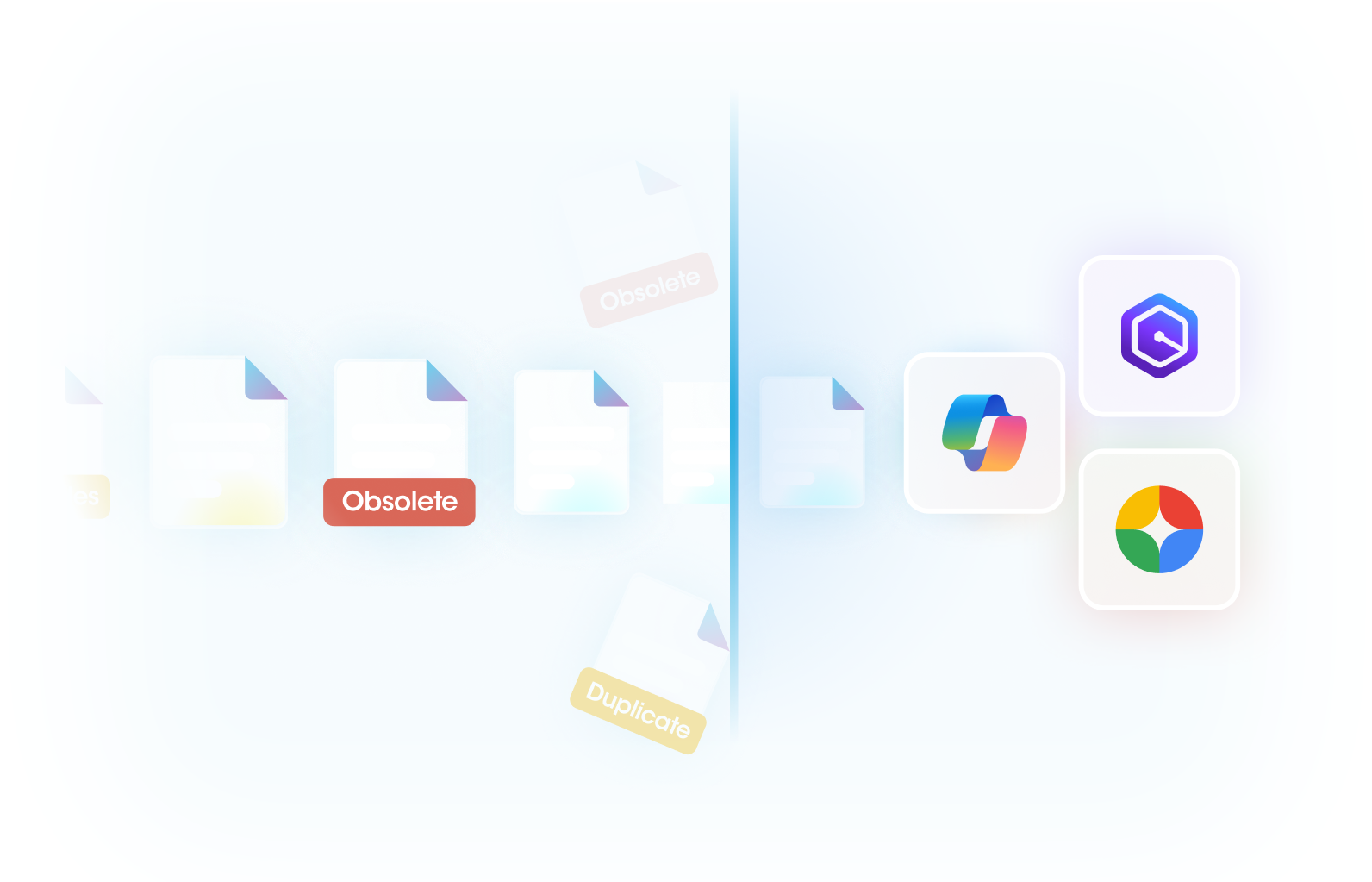
Minimize Redundant & Obsolete Data
- Automatically identify redundant data, such as duplicate and near-duplicate files, using flexible graph-based policies and AI-powered clustering
- Detect obsolete files based on various attributes such as file content, age, access and modification activity, ownership and more
- Automatically label or quarantine redundant and obsolete files to ensure AI excludes them when generating responses
Example: AI Agent retrieves a 10-year-old HR file to answer employee onboarding queries