Proactive vs. Reactive: Why Threat Detection Alone Falls Short in Data Protection
In an era where digital transformation and AI adoption are accelerating at unprecedented rates, data is becoming the lifeblood of modern organizations. As enterprises rush to integrate AI into their products and services, the proliferation of unstructured data has introduced complex challenges, particularly in securing and managing sensitive assets.
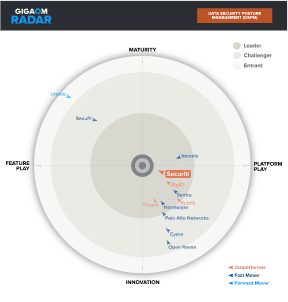
A growing reliance on threat detection over threat prevention, coupled with a lack of visibility into unstructured data, is creating significant risks for organizations. Without a clear strategy to identify and protect sensitive data, breaches can lead to severe financial penalties, regulatory non-compliance, and reputational damage. This blog explores these challenges and presents actionable solutions, including Data Security Posture Management (DSPM), to enable organizations to gain control of their data security.
The Problem: Shifting from Prevention to Detection
Organizations are increasingly focusing their security strategies on detecting threats after they occur rather than implementing measures to prevent them in the first place. While threat detection tools are essential, relying solely on them is insufficient to manage data risks effectively. Cyber attackers are constantly evolving their methods, exploiting gaps in security postures where preventive controls are weak or absent. By the time threats are detected, critical damage may have already occurred, particularly when sensitive data is compromised.
When it comes to data risks, a preventative approach is critical. This involves ensuring organizations identify and reduce redundant copies of sensitive data across the environment, proactively remediate vulnerabilities by applying appropriate security controls and retain only relevant sensitive data in assets with a healthy security posture, and ensure that access is restricted to individuals who genuinely need it. By taking these proactive steps, organizations can reduce the attack surface for sensitive data, minimize compliance risks, and build a strong foundation for managing data security.
The Unstructured Data Dilemma
The rapid adoption of AI has driven innovation but has also triggered a surge in unstructured data—files, emails, chat logs, videos, and more—spreading across organizational environments. This uncontrolled data sprawl creates a myriad of challenges:
- Hidden Sensitive Data: Critical assets containing personally identifiable information (PII), intellectual property, and other sensitive data often go unnoticed.
- Lack of Governance: Without proper classification and oversight, organizations struggle to manage and protect unstructured data effectively.
- Compliance Risks: Regulatory mandates (e.g., AU PA, GDPR, CCPA) require organizations to know where sensitive data resides and who has access to it. Unstructured data creates blind spots that increase the risk of non-compliance.
The urgency to address these challenges becomes even more evident during a cyber breach. Without visibility into their "crown jewels"—the most sensitive and valuable data assets—organizations are left scrambling to assess damage, risking hefty fines and reputational loss.
Cyber Breaches: When Unstructured Data Becomes a Liability
During a security incident, time is of the essence. Yet, many organizations lack the ability to:
- Identify where sensitive data resides across their environments.
- Determine who has access to that data.
- Assess whether it’s stored in vulnerable assets that attackers can exploit.
This lack of visibility into unstructured data significantly delays breach response efforts, increasing the scope and impact of the incident. For CISOs and CDOs, the inability to locate and protect sensitive data creates severe financial, operational, and reputational consequences.
The Solution: Data Security Posture Management (DSPM)
To address these challenges, organizations need a proactive solution that provides visibility, control, and security for sensitive data—both structured and unstructured. This is where Data Security Posture Management (DSPM) comes into play.
DSPM solutions enable organizations to:
1. Discover Shadow and Native Data Assets
A significant feature of DSPM solutions is their ability to uncover shadow data—unknown or unmanaged data assets that may exist within the organization without their knowledge. By identifying these hidden assets, DSPM tools help organizations mitigate risks associated with unmonitored and potentially vulnerable data.
2. Detect Sensitive Data Across the Organization
DSPM solutions automatically discover and classify sensitive data across all data environments, including cloud storage, databases, file systems, and collaboration tools. This eliminates blind spots and ensures that no sensitive asset goes unnoticed.
3. Correlate Data with Access Controls
It’s not enough to just know where sensitive data resides—organizations must also understand who has access to it. DSPM tools correlate data location with access permissions, ensuring that only authorized individuals can view or interact with critical assets.
4. Assess Security Exposure
DSPM solutions evaluate the security posture of assets where sensitive data resides, identifying:
- Misconfigurations that could expose data to attackers.
- Weak security controls that leave data vulnerable.
- Public exposure risks where sensitive data is unintentionally accessible.
By integrating DSPM into their data security strategy, organizations can:
One of the largest utility providers in Australia has successfully leveraged DSPM solutions to gain visibility into their sensitive data across their On-prem, Cloud and SaaS environments. By automatically cataloging unstructured and structured data across their organization, the DSPM solution has also helped them create a comprehensive data catalog. This catalog not only enhances data visibility but also empowers business stakeholders with actionable insights, ensuring better data governance and operational efficiency.