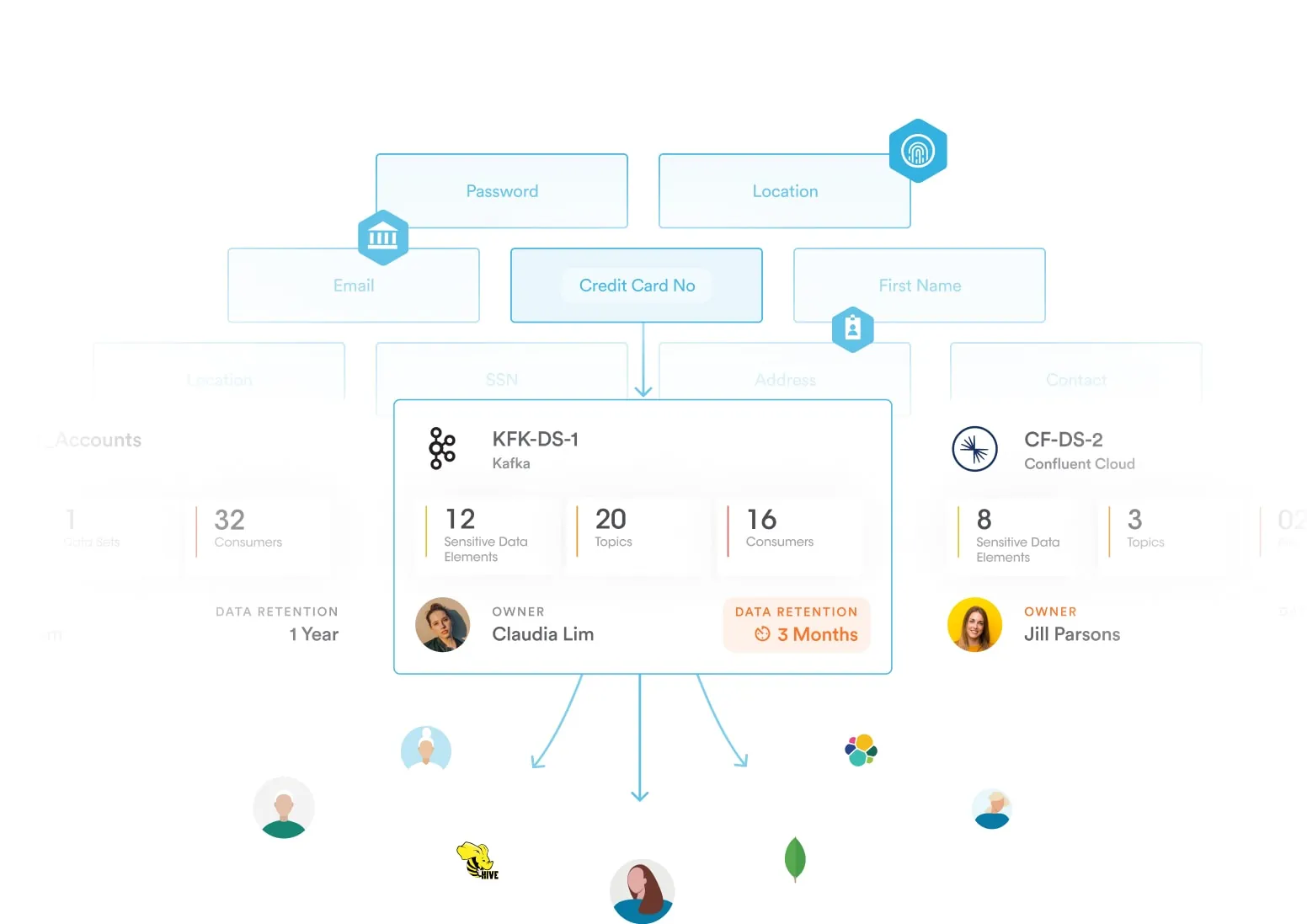
Data flows dynamically across your company, making data security posture management challenging for an organization. To tackle this, organizations must map data processing activities and understand data lineage. This helps visualize how data moves between systems, track duplicates, and trace data transformations across files and tables. By mastering this process, organizations can assess whether security and privacy controls apply consistently across data flows.
Modern applications also leverage data streaming technologies such as Kafka and Amazon Kinesis to listen to real-time data and make informed decisions. Securing such data flows is critical to prevent sensitive data sprawl downstream to consumers of data. Enforcing streaming topic-level access controls and masking sensitive data is essential for meeting data privacy and security obligations.
Building a Data Command Center With Built-in DSPM
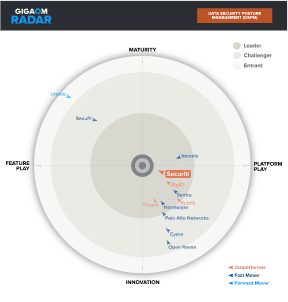
While a DSPM program has many benefits, enterprises are finding that early DSPM approaches that focus solely on public cloud tend to be insufficient. Additionally, many of these solutions which often rely on simple pattern matching for data classification are hindered by false positives and too siloed for overall enterprise data security and unified data controls.
In contrast, Securiti’s Data Command Center provides a much richer approach to DSPM with real-time contextual insights that enhance continuous data security posture across hybrid multicloud environments with more accurate data classification driven by AI. The Data Command Center also supports Data Security Platform (DSP) functions, AI Governance, and unified controls for Data Privacy, Governance and Compliance.
Securiti's Data Command Center empowers Fortune 1000 companies to protect data everywhere, including multiple public clouds, data clouds, on-premises, SaaS applications, and data flows. Securiti has been recognized by analysts such as Gartner and Forrester for its leadership and innovation in Data Security and Privacy Management.