Figure 5. Data Command Graph Provides Embedded Deep Visibility and Provenance for AI Systems
Typical Use Cases with Gencore AI and AI in Databricks
The support for Databricks' Mosaic AI and Delta Tables in Gencore AI enables enterprises to build safe, enterprise-grade AI systems that balance innovation with security and compliance. Key use cases include:
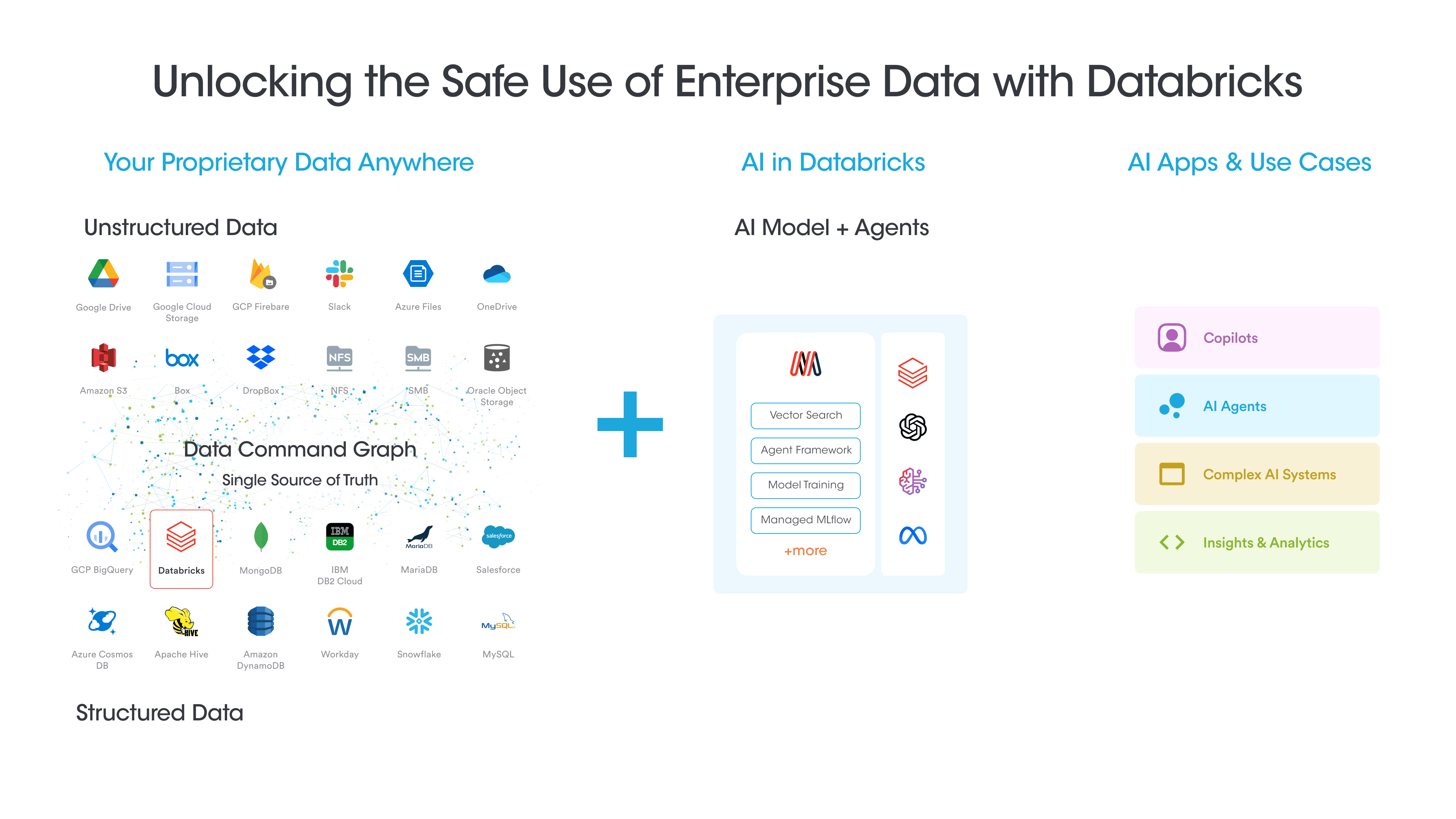
1. Securely Ingest Data from Diverse Sources for AI Intelligence in Databricks
The solution enables comprehensive data ingestion into Databricks Delta Tables through secure data pipelines.
- Seamlessly connect to on-premises databases, cloud storage platforms, SaaS applications (Salesforce, ServiceNow, Workday etc.), and on-premise data systems, enabling centralized data management in Delta Tables.
- Leverage Securiti's Data Command Graph to automatically select relevant datasets based on business context, metadata, and compliance requirements.
- Ensure data freshness, uniqueness, and topical relevance for high-quality inputs for AI model training and tuning.
- Automatically sanitize both unstructured and structured data, including redaction, masking, and anonymization based on data sensitivity levels and organizational policies.
- Monitor data flows for adherence to privacy regulations, security policies, and data sovereignty requirements.
These capabilities establish a robust foundation for secure, compliant data operations that power the AI model training and tuning within the Mosaic AI ecosystem.
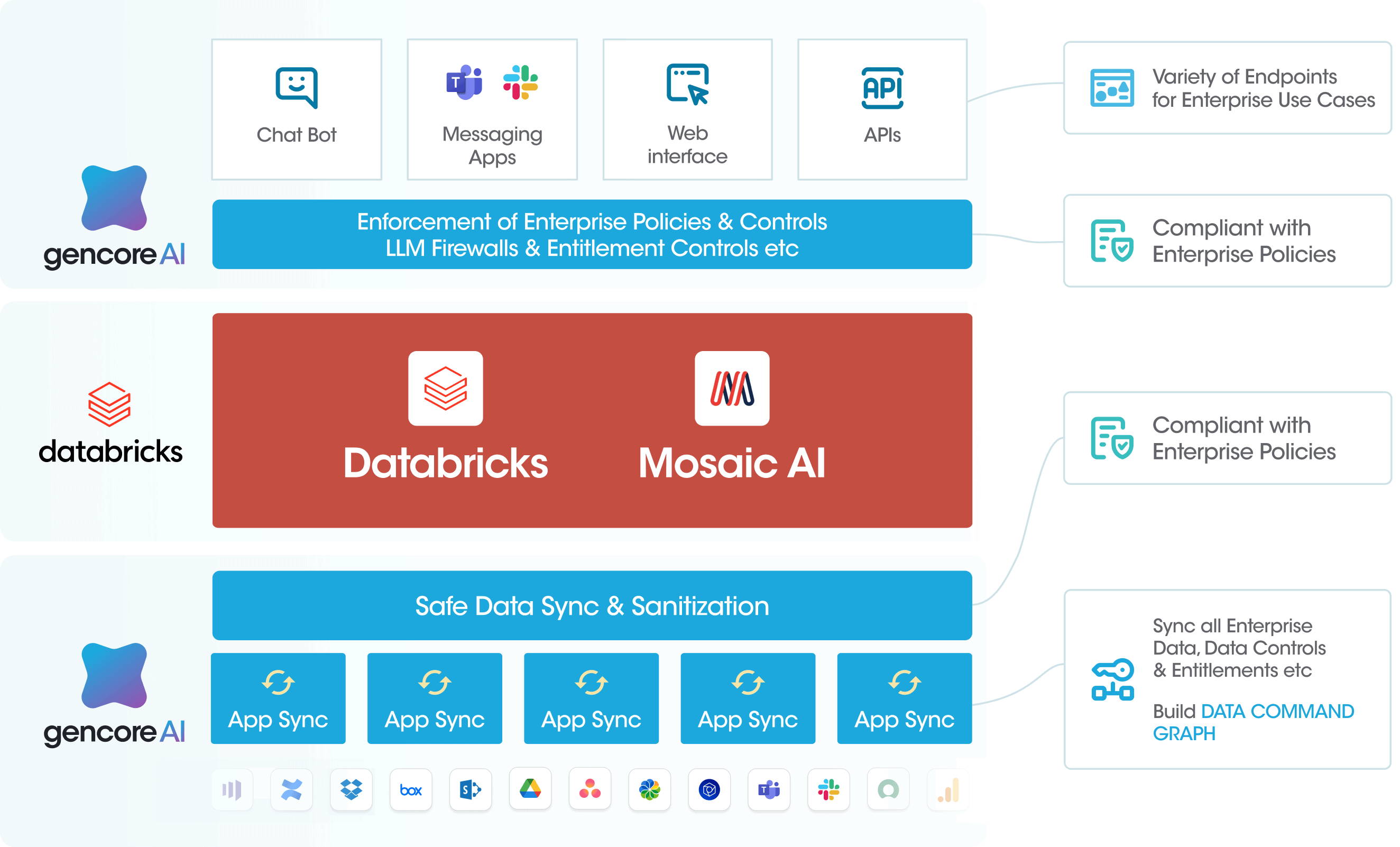
2. Provide Key Data Controls to Fuel the Scaled Use of Data + AI
The solution enables secure AI adoption at scale by implementing comprehensive governance controls and safeguards across AI and data systems, helping organizations confidently expand their AI capabilities while maintaining oversight.
- Enable alignment with OWASP Top 10 for LLMs for Safe AI Systems. Provide graph-based full provenance view of AI+Data, as required for various AI regulations.
- Enforce real-time data sanitization across AI pipelines in Databricks, automatically detecting and protecting sensitive information through masking and anonymization based on data classification policies.
- Provide user entitlement and regulatory information on data ingested into Databricks, along with access and entitlement graphs for data in Databricks.
- Provide LLM firewalls to ensure security and compliance with corporate controls on AI use, preventing prompt injection attacks, protecting against data leakage, and monitoring for adversarial inputs.
These controls enable organizations to scale enterprise AI initiatives while maintaining security, compliance, and governance requirements.
3. Building Personalized, Permissions-Aware AI Applications
Gencore AI provides a comprehensive framework for developing personalized, permissions-aware AI applications on the Databricks platform. The solution enables:
- Development of context-aware AI applications that automatically adapt to each user's permissions and entitlements, ensuring employees only access and utilize AI features appropriate for their role and clearance level.
- Seamless integration of enterprise data governance with AI workflows through automated access controls, real-time permissions validation, and granular audit logging - creating a foundation for responsible AI development.
- Creation of personalized AI experiences by leveraging rich user metadata, interaction patterns, and historical usage data while maintaining strict security boundaries and compliance requirements.
This enterprise-grade approach allows organizations to build sophisticated, user-aware AI applications on Databricks while preserving security controls and regulatory compliance at scale.
At Securiti, our mission is to enable enterprises to safely harness the incredible power of data and AI. Gencore AI's support for Databricks' Mosaic AI and Delta Tables enables organizations to use their proprietary data for AI model development and deployment - from model training and fine-tuning to custom LLM creation and production inference. This integration helps organizations move quickly and safely from proof of concept to enterprise-grade AI systems.
Interested in seeing a demo? Submit a demo request at Gencore.AI.