How DSPM Complements CSPM & SSPM
CSPM is an efficient solution that identifies and configures security vulnerabilities in the cloud while enforcing security best practices. However, it is a cloud infrastructure-centric tool. Hence, it treats all cloud resources alike without being able to prioritize assets with sensitive and high-risk data. This tends to lead to false positives and alert fatigue.
For example, a CSPM in a fintech company detects two misconfigurations in its environment. First, it detects an unencrypted customer database, and second a publicly accessible development server. While the first vulnerability requires immediate attention as it involves protecting the sensitive data of customers, the second is a low-priority risk since the server is used internally for testing purposes. However, the CSPM solution treats both misconfigurations with equal priority, creating a flood of notifications. Such situations result in overwhelming security teams, creating alert fatigue and causing delays, which could lead to data breaches or compliance risks.
Similar to CSPM, SaaS security posture management tools don’t always prioritize applications based on sensitive data but on risks associated with applications. For example, an SSPM tool may assign the same priority to a misconfiguration in an application that handles customer support tickets as it does to a critical risk in an application that processes financial transactions. Such skewed prioritization puts organizations at serious security, privacy, and compliance risks.
Conversely, Data Security Posture Management (DSPM) deals with the management and security of data within public cloud environments. DSPM gives comprehensive insights into data, such as its type, geographies, sensitivity, lineage, quality, and access usage over time. By leveraging these insights, security teams can optimize their data security posture across environments, such as preventing unauthorized access, masking data for secure data sharing, or complying with privacy regulations, especially cross-border transfers, to prevent compliance risks.
A robust DSPM solution complements both the CSPM and SSPM solutions, enabling security teams to prioritize vulnerabilities in cloud resources and SaaS applications based on the sensitive data within those assets. Consequently, security teams can reduce false positives and unnecessary time delays.
How Securiti Can Help
Securiti’s Data Command Center, with the integration of Data Security Posture Management, bolsters organizations’ security posture by securing their data everywhere. The solution provides the best of DSPM capabilities by offering contextual insights around data at rest and in motion. It helps establish robust access governance policies and controls, map data movements across systems and applications, prioritize misconfigurations based on sensitive data, and track data transformation across its lifecycle.
However, the Data Command Center goes beyond the traditional DSPM, which is limited to public clouds. Based on a unified framework, the solution helps protect data across public clouds, private clouds, data clouds, and SaaS environments.
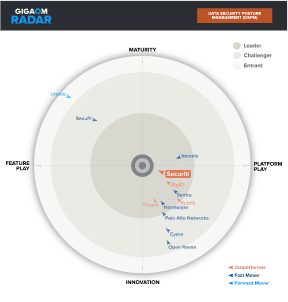
Notably, Securiti has been rated #1 by GigaOm Radar and Gartner’s Customer Choice reports for its state-of-the-art DSPM solution.
Request a demo to see Securiti’s Data Command Center™ in action.
Frequently Asked Questions about DSPM vs. CSPM vs. SSPM: