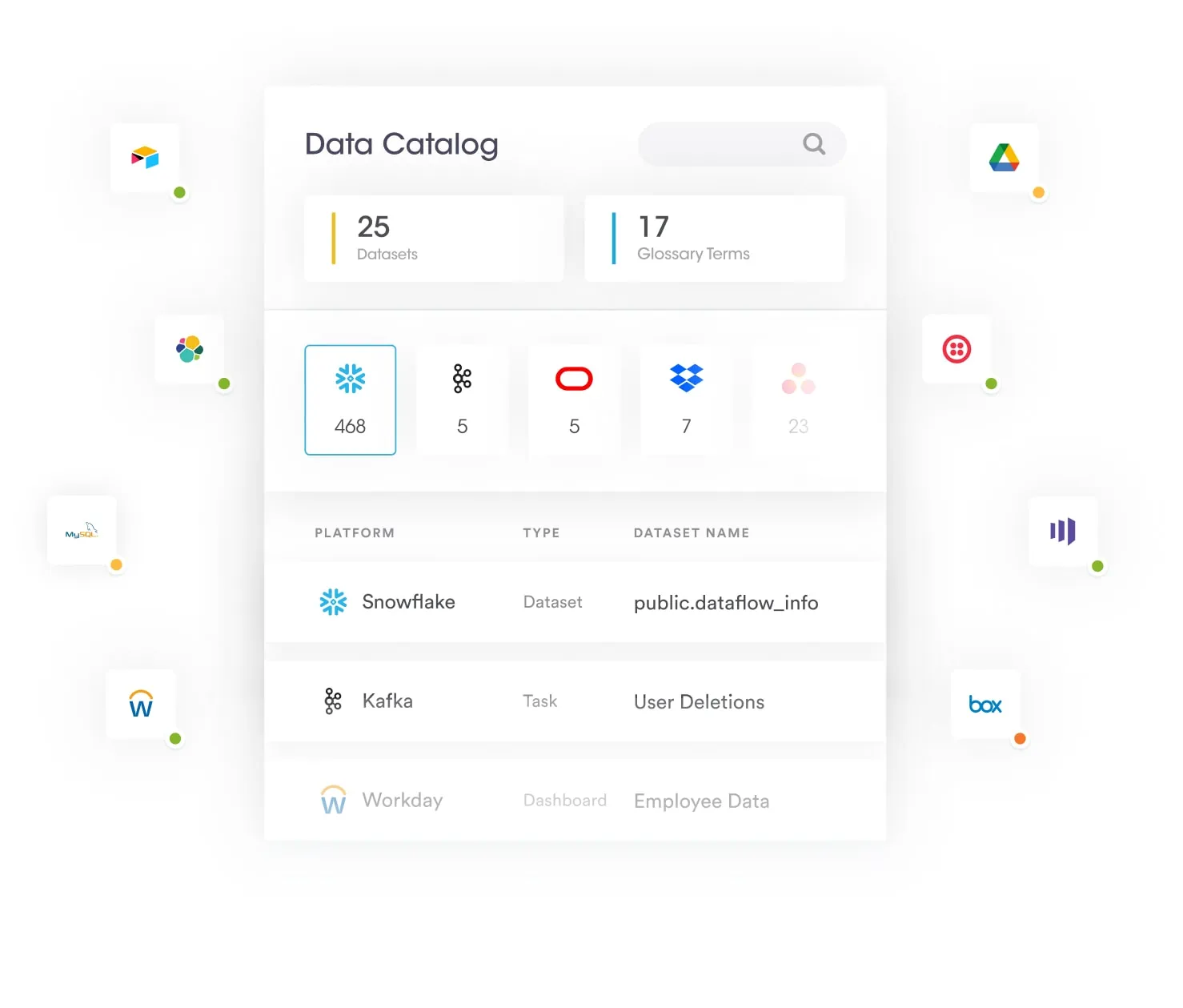
Rather than rely on business users to manually register data assets, organizations should leverage automated data discovery and classification to build a robust metadata management framework that provides insights into the data. The framework can enable organizations to automatically catalog what data exists, where it resides and provide rich metadata context, such as the data type, freshness, meaning, intended use, and sensitivity. It is also critical for the framework to address all data assets, including on-premises systems, SaaS applications, IaaS, and cloud data lakes and warehouses. Whereas traditional approaches focus on structured systems, the vast majority of data now resides in unstructured systems, which are important to include. An automated data catalog is the foundation for a modern metadata management framework that reduces labor and effort, increases accuracy, enhances granular insights and ensures broad coverage.
In playing the role of the centralized repository, a data catalog provides the single source of truth around corporate data. At its core, a data catalog should be able to answer broad scope of questions such as:
- Where can I find a specific piece of data?
- Where did the data come from?
- What is the end-to-end lineage of data?
- What is the business meaning of a specific data element?
- How fresh and up-to-date is my data?
Enable data security and privacy governance
Ideally, a data catalog should play a much broader role than just provide information on what data you have and where. It should also answer questions around privacy, security, and governance, such as:
- What data is sensitive?
- What are our retention policies around data?
- How do I access specific data for compliance audits?
- Can I use this data per company policy?
By answering these questions, a data catalog provides critical context to business users, enabling them to decide whether a particular dataset can be used in line with data privacy, security, and governance policies.